Rohit Rana
Editor-in-Chief & Lead Cybersecurity Analyst
Rohit is the driving force behind CyberPings' mission to demystify global cybersecurity news. With a deep focus on threat intelligence mapping, malware analysis, and zero-day exposure tracking, Rohit reviews and contextualizes complex cyber incidents to make them actionable for both industry professionals and the general public.
Editor-in-Chief
Threat Intel
Tech Communicator
Latest Reviews & Editorials

Malware Newsletter Round 91 - Latest Threats and Insights
The latest malware newsletter reveals new threats like Infiniti Stealer and npm supply chain attacks. Developers and organizations must stay alert to evolving risks in cybersecurity.

Researchers Roast Cybercriminals to Diminish Their Glamour
Researchers are roasting cybercriminals to diminish their glamor. This humorous approach aims to expose their failures and fracture trust within criminal networks. It's a fresh take on cybersecurity, focusing on education and awareness.

Syria’s Security Failures Exposed by Government Account Hack
A recent hack exposed Syrian government accounts, revealing significant cybersecurity weaknesses. This incident raises concerns about the state’s digital security practices and its ability to communicate effectively. Experts warn that without urgent reforms, Syria's digital infrastructure remains at risk.
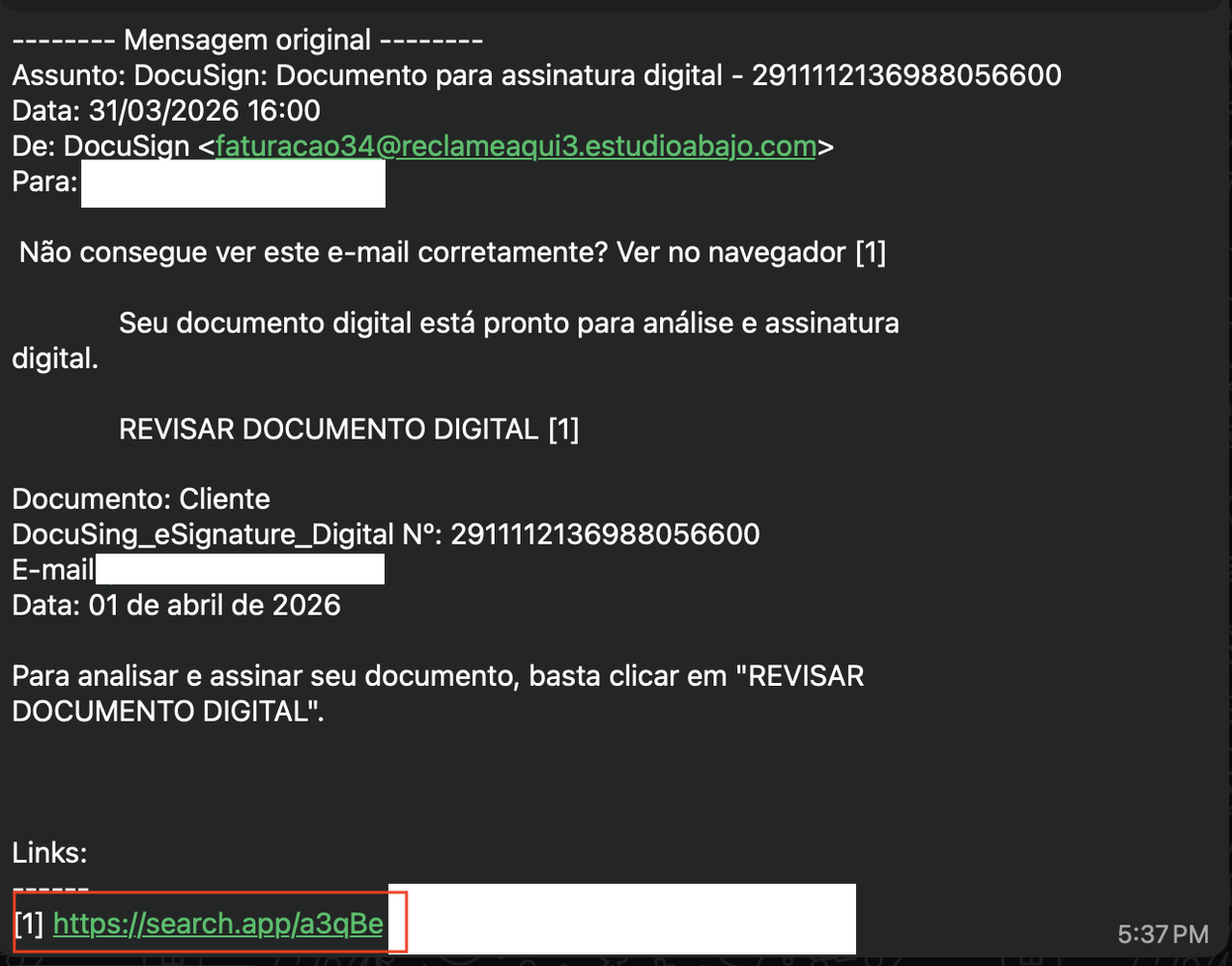
Malicious Email Delivers CMD Malware - Privilege Escalation Alert
A malicious email has delivered a .cmd malware file that escalates privileges and bypasses antivirus systems. Users are at risk of significant system compromise. Awareness and immediate action are vital to mitigate this threat.

Anjali Hansen - Emphasizes Cross-Team Collaboration in Privacy
Anjali Hansen shares her career journey and the vital role of cross-team collaboration in cybersecurity. Her insights highlight how teamwork strengthens data protection efforts across organizations.
Axios NPM Package Compromised - Supply Chain Attack Exposed
A major supply chain attack compromised the Axios NPM package, affecting millions of users. Malicious versions deployed a RAT, posing serious security risks. Swift action was taken to remove the threats.

Device Code Phishing - Attacks Surge 37 Times in 2026
Device code phishing attacks have skyrocketed this year, with a 37x increase. Users of IoT and streaming devices are particularly at risk. New phishing kits like EvilTokens are making these attacks easier for cybercriminals. Stay alert and protect your accounts.

Node.js Maintainers Targeted - Sophisticated Social Engineering Scheme
A coordinated social engineering scheme is targeting Node.js developers, risking the integrity of widely used software packages. This alarming trend highlights the need for vigilance in the open-source community.

Fortinet FortiClient EMS - Critical 0-Day Vulnerability Exploited
A critical zero-day vulnerability in FortiClient EMS is actively exploited. Fortinet has released emergency patches and urges immediate action from users.

Cybersecurity Veteran Mikko Hyppönen Now Hacking Drones
Mikko Hyppönen, a cybersecurity pioneer, is now tackling the threats posed by drones. His shift from fighting malware to drone defense highlights the evolving landscape of cybersecurity. With increasing drone use in conflicts, understanding these threats is crucial for safety.

Transparent Tribe Targets India's Startup Ecosystem - New Threat
Acronis reveals that Transparent Tribe is now targeting India's startup sector, especially cybersecurity firms. This shift raises concerns about espionage and data security risks. Startups must bolster their defenses against these sophisticated attacks.
.webp)
Best User Access Management Tools - Top Picks for 2026
Explore the best user access management tools for 2026! These tools enhance security and streamline user permissions, helping organizations protect sensitive data and ensure compliance.

Anthropic Ends Claude Subscriptions for Third-Party Tools
Anthropic has halted third-party access to Claude subscriptions, significantly affecting users of tools like OpenClaw. This shift raises costs and limits integration options, leading to dissatisfaction among developers. Users must now adapt to new billing structures or seek refunds.

Job Scams - Coca-Cola and Ferrari Offers Are Traps
Scammers are impersonating Coca-Cola and Ferrari with fake job offers to steal your passwords. Job seekers are at high risk as these scams become more sophisticated. Protect your personal information by verifying job offers directly with companies.
FAA Drone Restrictions - First Amendment Rights Under Attack
The FAA's new drone restrictions threaten the First Amendment by criminalizing the filming of ICE and CBP activities. This unprecedented move raises serious legal concerns. EFF and journalists are pushing back against this infringement of rights.

Gaming Industry - High-Stakes Cybersecurity Threats Explained
Cybercriminals are increasingly targeting the gaming industry, driven by financial transactions and sensitive data. As casinos go digital, understanding these threats is vital for operators to safeguard their assets.

Brokk Hacked - Play Ransomware Exposes Sensitive Data
Brokk has reportedly been hacked by Play ransomware, leading to the leak of sensitive corporate data. This incident could severely impact the company's reputation and security. Organizations must bolster their defenses to prevent similar breaches.

Inconsistent Privacy Labels - Users Left in the Dark
Data privacy labels for mobile apps are intended to inform users, but they're currently inconsistent and unclear. This leaves users unsure about how their data is being handled. It's crucial for developers to improve these labels to enhance user trust and security.

Elastic Security - Nine New Integrations Announced
Elastic Security Labs just launched nine new integrations! These tools boost cloud security, endpoint visibility, and email threat detection, helping teams respond to threats faster.
Jurassic Fish Chokes on Squid - A 150-Million-Year-Old Fossil
A 150-million-year-old fish fossil reveals it choked on a squid-like creature. This discovery highlights ancient marine life interactions and extinction events. Explore its significance today.

LinkedIn - Secretly Scans 6,000+ Chrome Extensions
LinkedIn is scanning over 6,000 Chrome extensions to collect user data, raising significant privacy concerns. This could expose sensitive information about users and their corporate affiliations. Stay informed and protect your privacy.

Network Security - Understanding the Complexity Crisis
Network security is facing a complexity crisis due to ineffective policy governance. This impacts compliance and increases vulnerabilities. Organizations must adopt better governance strategies to protect their networks.

Chaos Malware - New Targeting of 64-bit Linux Servers
Chaos malware has evolved to target 64-bit Linux servers, expanding its attack surface. This shift raises alarms for organizations relying on these systems. Enhanced security measures are now crucial to protect against potential larger-scale attacks.

Video Conferencing Bug - CISA Orders Agencies to Patch
A serious vulnerability in TrueConf video conferencing software is being exploited by Chinese hackers. CISA has mandated a two-week patch deadline for federal agencies. Immediate action is essential to safeguard sensitive data and communications.