Real-Time Carbon Tracking - Securing Manufacturing Systems
Basically, we need to protect carbon tracking systems in factories to keep data safe and reliable.
Manufacturers are urged to secure real-time carbon tracking systems. This integration is vital for compliance and operational efficiency. A proactive approach can turn carbon data into a valuable asset.
What Happened
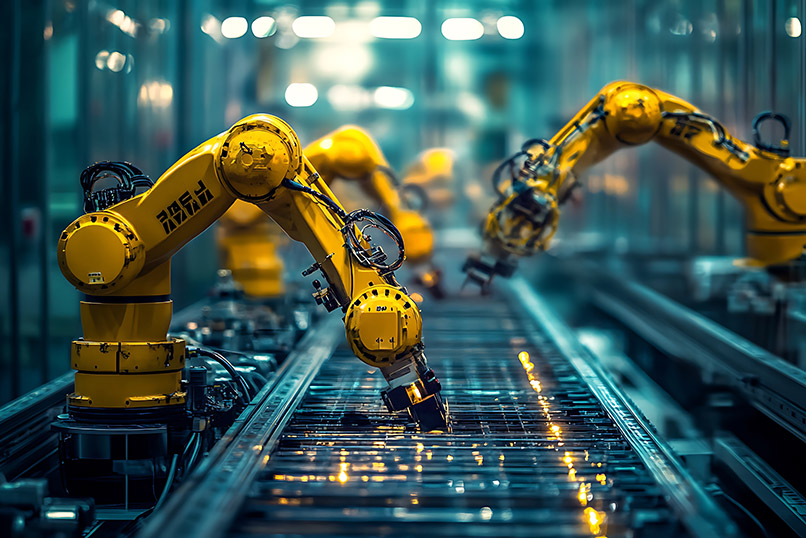
Manufacturers are increasingly required to provide real-time emissions data that is auditable and meaningful. This shift moves carbon telemetry from after-the-fact reporting into the operational control plane of production systems, changing the security landscape. As companies integrate carbon monitoring into their manufacturing execution systems (MES), they must address new security challenges to prevent disruptions and ensure data integrity.
The approach developed by industrial AI specialist Lesia Yanytska introduces the Agentic Manufacturing Systems (AMS) framework. This framework emphasizes the importance of embedding carbon intensity monitoring securely within MES to create a trustworthy operational capability. By treating carbon data as an integral part of the production process, manufacturers can enhance compliance with regulatory demands while maintaining operational efficiency.
Core Security Priorities
Integrating carbon intensity monitoring into MES requires a clear set of security priorities. These should be treated as essential design constraints rather than optional features. Key areas of focus include:
- Device and Protocol Security: Carbon sensors and edge gateways must be treated as industrial endpoints. This means employing secure industrial protocols, such as certificate-based authentication and encryption, to ensure that telemetry is authenticated and confidential. Implementing end-to-end signing and tamper-evident logs is crucial for maintaining data provenance.
- Preserving the OT Perimeter: Carbon data should flow through established operational technology (OT) channels, ensuring it does not become a new entry point for attacks. By maintaining a hardened perimeter through segmentation and DMZs, manufacturers can protect their systems from potential threats.
- Risk at the Decision Layer: When carbon metrics influence autonomous systems, the risk shifts to decision logic. It's vital to enforce immutable governance rules and maintain explainable audit trails to ensure that any actions taken based on carbon data are legitimate and safe.
Operational Controls and Supply-Chain Hygiene
Security in manufacturing relies not only on architecture but also on processes. Secure provisioning, authenticated firmware updates, and strict access controls are essential to mitigate supply-chain risks. Continuous monitoring that correlates carbon telemetry with network indicators can help detect manipulations that might otherwise go unnoticed.
Organizations must also engage in third-party risk management, ensuring that suppliers adhere to stringent security standards. This includes requiring contractual commitments to security controls and regular attestations. Incident response plans should explicitly address scenarios where emissions data could be weaponized to influence production.
Regulatory Alignment and Practical Deployment
As regulatory pressures increase, manufacturers must align their carbon monitoring systems with industrial security standards. By embedding governance at the decision layer, companies can meet both operational and compliance demands effectively. The key takeaway is that sustainability data must be engineered as OT data from the outset to reduce friction with auditors and regulators.
By focusing on protocol-level security, device attestation, perimeter preservation, and robust governance, manufacturers can transform real-time carbon tracking from a potential liability into a reliable operational asset. This proactive approach not only enhances compliance but also supports efficient production processes.